Understand the risks of working and studying online and how to mitigate them
All University staff, College staff, students and other users who use University information services must complete the University’s cyber security awareness training every year, according to the University's Information Services Acceptable Use Policy.
The training course is hosted on the MyCompliance e-learning platform. You will receive emails from no-reply[@]metacompliance.com on behalf of the University asking you to complete the course each year, as well as several reminders. You can verify that the emails you receive are genuine by comparing them with examples on this website.
Logging in to MyCompliance
You can either follow the link to the course in the email you receive or, if you prefer, log in to MyCompliance independently and find the course on your homepage.
You should log in with your University identity – that is, your [CRSid]@cam.ac.uk email address and University account password (formerly called Raven).
If you are logged in to Microsoft 365 with your institutional email address – for example, @medschl.cam.ac.uk – you may get an error message or will not see your course listed. You may want to use a separate private or incognito browser window to log in with your University account. Alternatively, you can log out of your institutional account and log in again with your University account.
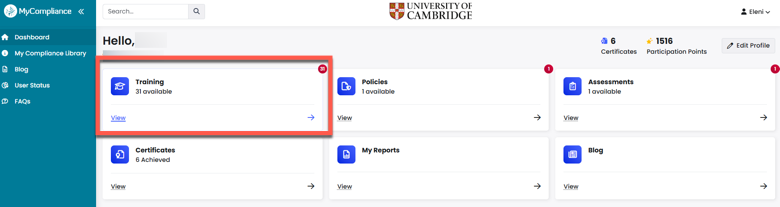
Access your outstanding training
You can access any outstanding/incomplete training by selecting the 'Training' tile on the MyCompliance homepage.
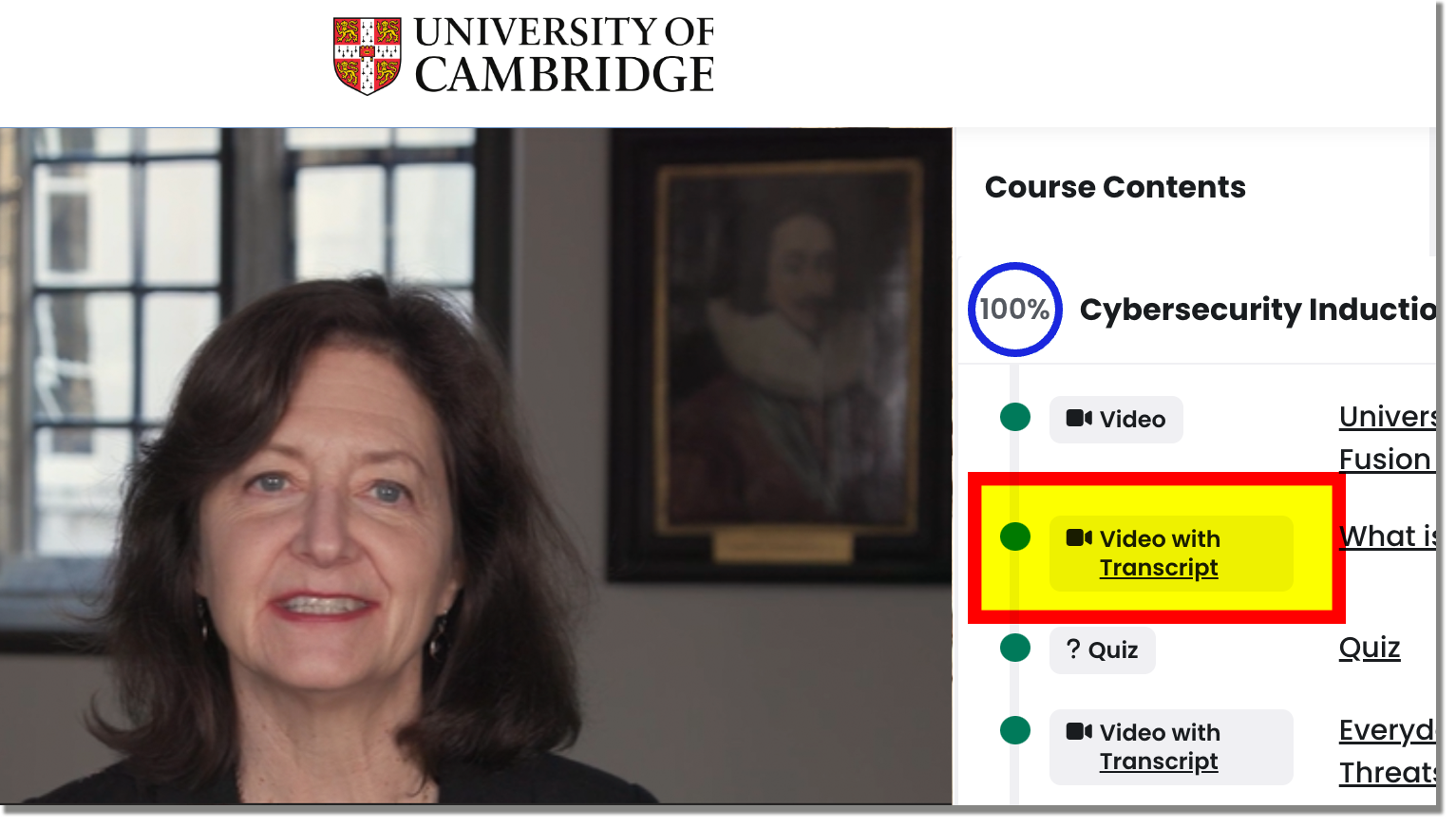
Download a course transcript
Select the 'Transcript' link in the 'Video with Transcript' module in the 'Course Contents' tab to download a course transcript:
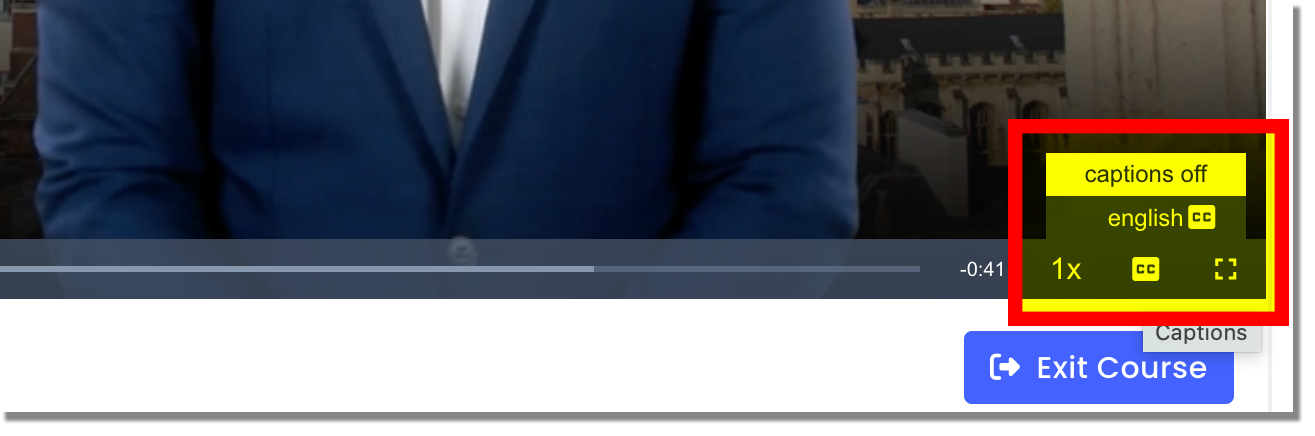
Enable captions
Select 'CC' in the bottom right of the video player toolbar and select 'english CC' from the pop-up menu to display captions during playback of the videos in the course:
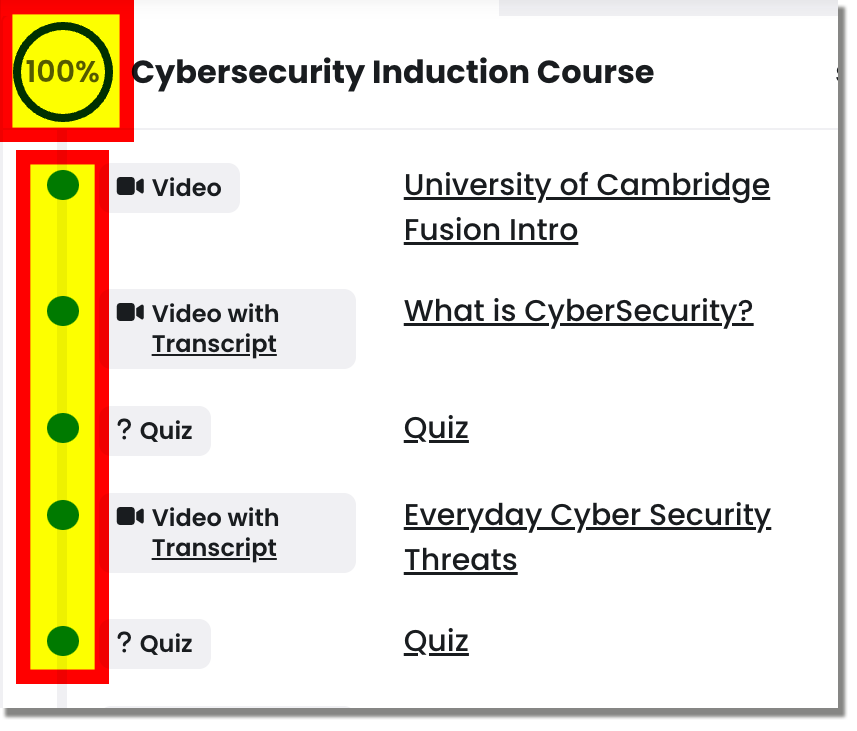
Check you have completed all the course modules
Check the 'Course Contents' tab to make sure you have achieved 100% completion for both Part 1 and Part 2 of the course. All the dots beside the modules should be green, not grey, and you will see your completion score in the circle at the top:
Questions about our cyber security training
If you have any queries or feedback about the training, please contact the UIS Service Desk.
Additional resources to supplement the training course
We recommend reading this additional University guidance and advice.
A student guide to scams
Passwords, passphrases, password management software
Multi-factor authentication
Information assets
- How to back up data securely
- How to store and share personal data
- Guidelines on University data security classifications
Phishing
Best practices when using your own device
- How to add another user account
- How to check if your laptop is encrypted
- How to keep your operating system updated
- Information security best practice for working from home
- Antivirus software